If you’re aspiring to become a professional in the field of computer security, wish to understand further the current threat landscape or simply want to have a play around with some toys then it sounds like you want to set up a Honeypot. If you’re unsure what a honeypot is then Wikipedia defines it as:
In computer terminology, a honeypot is a computer security mechanism set to detect, deflect, or, in some manner, counteract attempts at unauthorized use of information systems. Generally, a honeypot consists of data (for example, in a network site) that appears to be a legitimate part of the site but is actually isolated and monitored, and that seems to contain information or a resource of value to attackers, which are then blocked. This is similar to the police baiting a criminal and then conducting undercover surveillance, and finally punishing the criminal.
In this article we’re going to be running through the process in which you can set up your own Honeypot using a prebuilt tool referred to as the Modern Honeypot Network.
Requirements and Assumptions: In regards to this tutorial it is assumed that you already have a medium to strong understanding of the Ubuntu command line interface and understand its basic functions. You will also be required to have set up a DigitalOcean account (Use this referral link for $10 credit) as well as an AWS account. As a side note to set up a DigitalOcean server you will need to spend at least $5.
Outcome: By the end of this tutorial you should have created a command server with at least one sensor attached to it, all being created by using tools provided by the Modern Honeypot Network.
Stage 1- Digitalocean and an Ubuntu server.
In this stage you will be setting up an Ubuntu server on Digitalocean. At the end of this stage you should have a fully working server running the Ubuntu operating system and should have received a confirmation email from DigitalOcean. You can achieve this by following the below steps:
Stage 1.1 – Creating a droplet
First you will need to sign into your DigitalOcean account with the username and password you entered on creation.
Now you will need to set up your droplet, in this instance we will be using the bare minimum required to run our server. First off you will need to choose the underlying operating system for your command server. Once we have finished we will be using a website GUI front end so the underlying OS is not overly important, however in this instance we will be using Ubuntu (Make sure this is the version specified in the image to the right) .
Next we will be choosing the specifications of our command server. This server will be taking the information given to it by our sensors and in turn will not be performing any overly complicated tasks. That being the case it is a good choice to choose the least expensive option in this regard. That being the case in this instance we will choose the ‘$5/mo’ option.
The final option that we will be dealing with on this setup page is the location in which our server is based. It is best to choose a location that is closer to where you will be primarily dealing with the server however this choice is up to you. As HackingInsider works out of the UK we will be selecting London.
Finally you will be presented with several additional options, in regards to this instance we will not be using any of these and we can now simply move onto creating our droplet. To do so select ‘Create’. After which you may need to set up your payment information depending on if you have done so in the past.
After the above has been completed you will be emailed the details for your new server of which you can take forward to the next stage. The above is required due to the necessity of having a command sever that our AWS sensors will communicate with. On average the above process should take around 5 to 10 minutes to complete.
Stage 2 – Setting up the control server:
Now we have set up the backend for our server we will now need to add the Modern Honeypot Network (MHN) framework to our server. At the end of this you should have a fully working Honeypot with a working GUI web front end. This can be achieved by following the below steps:
Stage 2.1 – Installing a command line interface tool:
For the remainder of this tutorial we will be using the command line interface (CLI) on Ubuntu, that being the case we will need a tool we can use to operate this. In this instance I will be using a tool called Putty, which is a free tool that can be used for an array of tasks.
Once you have downloaded putty off their website you can launch it like any other .exe program.
Stage 2.2 – Accessing your server and installing MHN:
After you have completed the above you will need to enter the IP that you were emailed by DigitalOcean into the section on Putty that asks for ‘Host Name (or IP address)’. After you have done this, select ‘Open’. You will be taken to a CLI of which you will be asked to enter the server’s username and password (These would have also been emailed to you). After so you will be asked to change the server’s password.
You will now have access to your server and in turn its CLI. The next step of which will be to install the needed software to run the Modern Honeypot Network. Once here you will need to enter the following commands in order, dealing with any errors that occur accordingly.
sudo apt-get upgrade sudo apt-get update cd /opt/ apt-get install git -y git clone https://github.com/threatstream/mhn.git cd mhn sudo bash install.sh
Eventually you will be greeted with a prompt asking for you to enter an array of questions for your Honeypot. These will depend solely on what you want to set them as, however see the image below for an example of an input.
After the above the script will continue to configure the Modern Honeypot Network setup and will take a sizable amount of time. During this process you will also be asked if you want to integrate the honeypot with Splunk, for simplicity we will select ‘no’ in this instance.
After the installation has taken place you will then be able to visit your server via a web browser. If you point your webbrowser to the IP address sent to you by DigitalOcean you will be able to access your server’s web GUI.
This stage was required to set up MHN on your main command server and to create the GUI interface you will use day to day. This stage will take approximately 30 minutes due to the installation time.
Stage 3 – Deploying sensors:
In this stage you should finish the completion of your Modern Honeypot Network setup. After this stage you should have set up at least one sensor (based off AWS) that will communicate back to your command server. You can achieve this by following the below steps:
Stage 3.1 – Set up an AWS instance:
After creating your AWS account you will be directed to a screen detailing an array of Amazon Web Services, on this screen you are looking for the one labelled EC2. After which you will need to locate the button labelled ‘launch instance’.
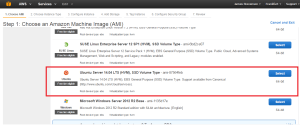
When launching this instance you will need to follow very similar steps to previously when working with Digitalocean. First you will need to select the operating system you wish to be installed on the server, in this case we will be using Ubuntu.
Next you will continue through the setup process selecting the next button as appropriate, this being until you reach the ‘Step 6: Configure Security Group’ page. On this page you will create a security group that allows for traffic to access the server from any IP address.
After you have done this you can review your setup and then finally click ‘Launch’. Once you have selected this you will be asked to make a ‘Key pair’. Once you have created your key pair you will need to download it.
After you have completed the above stages you will have set up an AWS server and can view it by selecting the ‘instances’ button.
Stage 3.2 – Accessing your instance via Putty:
As Putty does not accept the default .pem key files that AWS creates we will need to convert it. You can do this by using the tool puttygen.exe of which should have been downloaded along with putty. Once opened you will need to select the ‘Load’ button and find your .pem key. You will then need to select ‘Save private key’ and save it as the same name as your key was on AWS.
After you have done this you will need to open up Putty again and go to ‘Category’ > ‘Connection’ > ‘SSH’ > ‘Auth’. Once here you will need to ‘Browse’ to your newly created key file.
Once you have done this you will need to SSH into your Ubuntu server, do this by following the image below.
After you have SSHed into the server you will once again be confronted with a CLI of which should allow you to access your Ubuntu instance.
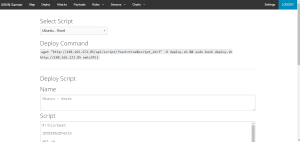
Stage 3.3 – Running the sensor Script:
Now you have a working AWS instance we can now run a Bash script on it to connect it to your command server. To do this you will need to sign into your command server via your website GUI and go to the ‘Deploy’ section. Once in this section you will need to select ‘Ubuntu – Snort’. In the ‘Deploy command’ section you will be presented with a script. Copy this script into your AWS CLI and wait for it to be completed. Once completed you can also choose ‘Kippo as vulnerable juniper netscreen’ and enter that into your CLI.
After you have completed this you’r Honeypot will now be fully functional and will begin to collect attack data from those who attack it. You can view this data from the website GUI interface. As a whole this stage should take approximately 10 to 15 minutes, with this whole tutorial coming to around 55 minutes all together.
James Stevenson
I’m a Cyber Security enthusiast that loves all things to do with technology. I’m specifically interested in cyber security and ethical hacking.
Full article:
http://www.hackinginsider.com/2016/03/whats-a-honeypot-and-how-to-set-one-up-in-under-an-hour/














Leave a comment