In my recent Darknet series, I attempted to connect the dots on the Deep Web. I covered the two largest anonymity networks on the Internet today, Tor and I2P. While my initial four articles were meant as an introduction, I ended up receiving a lot of interesting comments and messages asking the technical differences between the two. I’d like to thank all of you for letting me know what was on your minds, as you should always!
Back to Onions
Tor and I2P are both anonymizing networks, allowing people to tunnel out of their open and non-secure environments. However, they achieve this in slightly different ways.
As a quick recap, onion routing involves wrapping your packets in multiple layers of encryption, in a system where each router that passes it along only has the key to decrypt its layer and none of the others. This way, each router can only see the router that sent it the packets and the router it in turn must send the packets to. It’s how this is performed that draws its contrasts. Let’s take a look at each in more detail.
Tor
Tor has been around quite a while longer then I2P. As a result, it has been studied much more in depth by both the white hat and black hatcommunities. In my Tor article, I mentioned it was better designed as an out-proxy than I2P is. This is because there are many more exit nodes on the Tor network then on I2P, and with the ability to use TLS and bridges, Tor also performs better at evading state-level firewalls (think China and Iran).
The only reason anyone would be changing the I2P config would be to set up port forwarding, and that’s a bit out of this article’s scope (though a great idea for a future one). Tor is a simple SOCKS proxy, so your only choice is to be a relay, exit node, or client node. Tor also has advantages in that it holds a large number of talented developers, some of them are even funded. In fact, Tor receives a good amount of money for its maintenance and development, and this shows in the form of its excellent documentation and white papers.
On that note, Tor is written in C, as opposed to I2P’s Java. This means that the Tor client typically runs faster and with a smaller memory footprint.
Tor takes the directory-based approach, providing a centralized point to manage the overall ‘view’ of the network, as well as gather and report statistics, as opposed to I2P’s distributed network model. This centralization reduces complexity at each node and can efficiently address Sybil attacks.
I2P
I2P was designed with the internal network in mind. Steps have been taken to provide a better environment for hosting services rather then providing out-proxies. This is the fundamental difference between I2P and the Tor network. I2P was designed and optimized for hidden services, which are much faster than in Tor, as the network is fully distributed and self-organizing. Helping this is the fact that peers are selected by continuously profiling and ranking performance, rather than trusting claimed capacity.
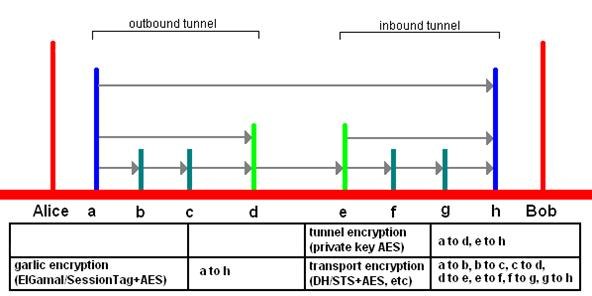
I2P is packet switched, instead of circuit switched, like the Tor network. This means transparent load balancing of messages across multiple peers, rather than a single path. Essentially, all peers participate in routing for others. Also along these lines, I2P’s API was created for anonymity, unlike SOCKS, which is designed for functionality. As Tor uses SOCKS, I2P tends to fare better for security than Tor, but keep in mind most people will not have a threat model where this would be of concern, as attacks tend to be highly complex.
Lastly, tunnels in I2P are short lived, decreasing the number of samples that an attacker can use to mount an active attack with, unlike circuits in Tor, which are typically long lived.
What Is Best for Me?
That’s a very open ended question. At times, it falls to a technical choice, an example being P2P file sharing over I2P, where as Tor does not support (nor encourage) it. Other times it depends on your personal choices. You will find the content on the Tor and I2P networks to vary. It is not to say you should not host services on Tor, or should not out-proxy with I2P, but the networks are designed with different strengths in mind.
Perhaps the answer to the question is what I do. I use both.
Generally, if you are looking for a robust SOCKS out-proxy, Tor is a great choice. Granted a number of exit nodes have been blacklisted to prevent abuse, the network still has plenty more.
If you want to host hidden services, then I2P would be your better choice, as you are afforded the added protection of decentralization and higher speeds to go along with it.
Shortfalls
Using these tools, you are only as anonymous as you allow yourself to be. Doing things like logging into your personal Facebook account or checking your personal email while using these networks will remove a good chuck of what is protecting you and keeping you safe. It’s wise to keep a few guidelines in mind:
- Think of your ‘clear’ net identity and your darknet identity as two separate things. Do not mix the two.
- Avoid using any personal information or distinguishing remarks on the network—remember to be someone else. Don’t leave clues as to who you really are.
- You should never use your normal browser to view resources through the networks, only use the bundled browsers, or manually turn off those services. Flash and Java are especially good at betraying your location and IP address to servers. Turn them both off.
Tor Exit Nodes
A brief word about exit nodes.
An exit node is a machine that sits on the edge of the darknet. It acts as an intermediary between yourself and the outside Internet. As such, the exit nodes are routing all sorts of unsavory traffic, pretty much all the bad things you might expect to find hidden on a darknet. While Tor does give you the option to function as an exit node, unless you wish to have a talk with the police, leave it alone.
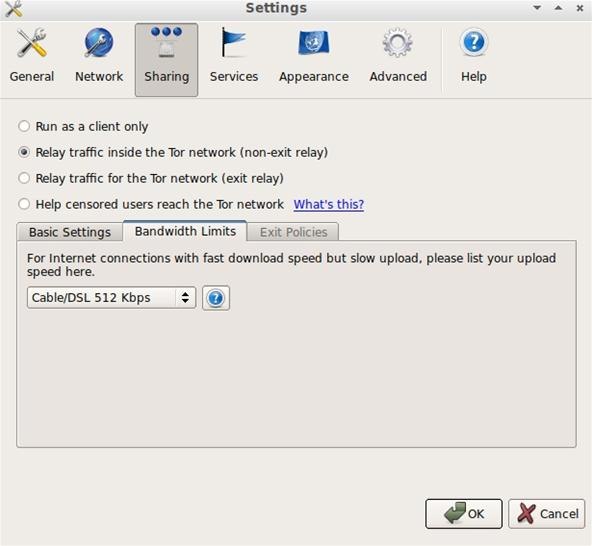
In this case, what you can choose is a non-exit relay. This lets you help with forming more random and unique routes on the network. Helping your mates browsing along with you by giving them more security all while speeding up your own traffic. Why you are on this screen, you can change your bandwidth settings to reflect your capabilities as well.
Now, I want to hear from you!
What do you use Tor and I2P for? Do you like one over the other? Why?

Leave a comment